Trezor Login – A Complete Guide to Secure Access
Learn how to safely perform Trezor Login, manage your crypto portfolio, and protect your private keys through the official Trezor Suite. Get detailed instructions, troubleshooting, and expert tips on secure wallet access.
🔑 Introduction to Trezor Login
Trezor Login is the authentication process that connects you to your crypto assets through the official Trezor Suite interface. It uses advanced hardware verification to ensure that only you, the wallet owner, can authorize transactions. This login process represents one of the most secure gateways in the crypto ecosystem.
Unlike centralized exchanges or online wallets, Trezor’s login doesn’t rely on passwords stored on servers. Instead, all authentication occurs offline — directly on your hardware device.
🧭 Step-by-Step Process for Trezor Login
Step 1: Connect the Trezor Device
Attach your Trezor Model T or Trezor One to your computer via the original USB cable to begin the login process.
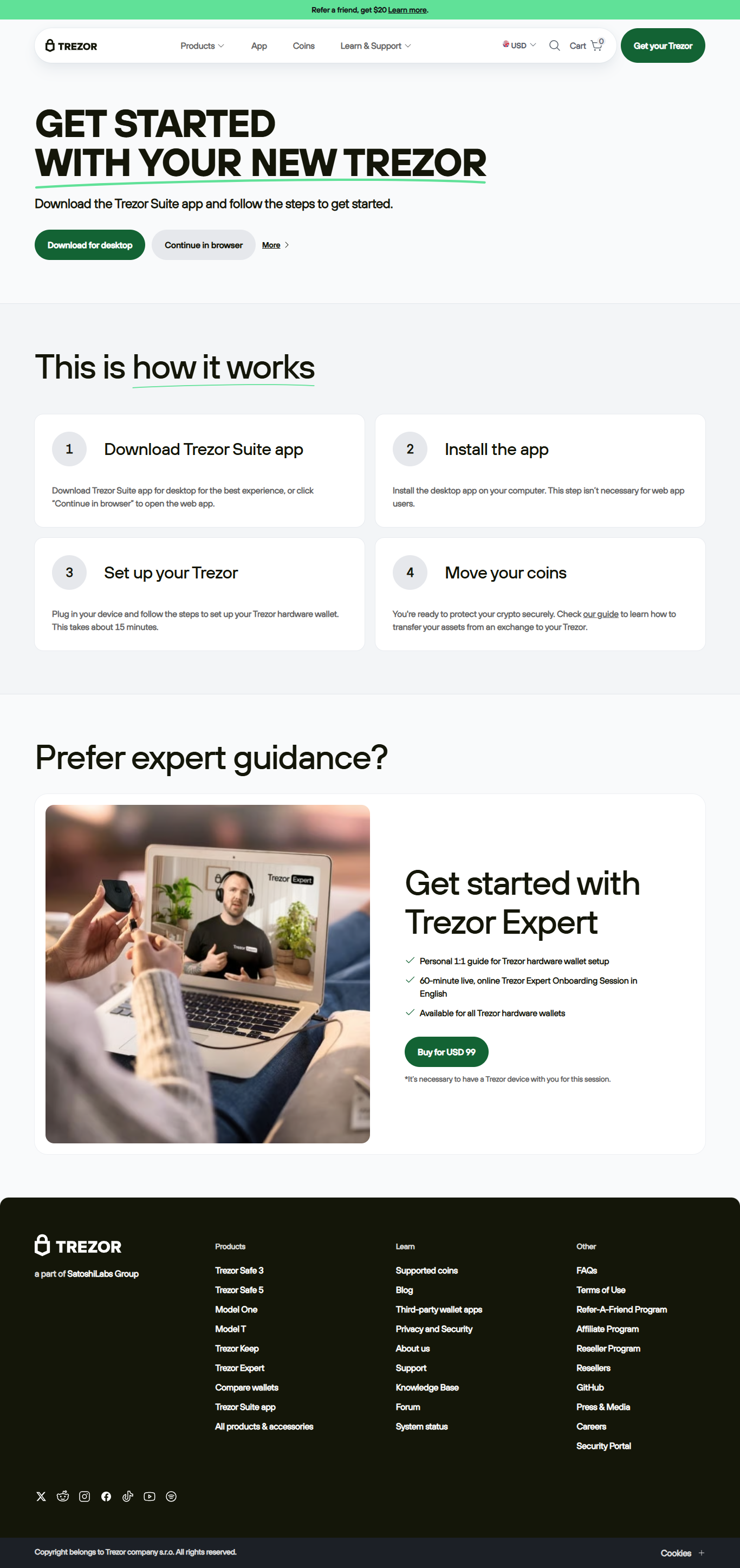
Step 2: Launch Trezor Suite
Open the official Trezor Suite app. Ensure it’s downloaded directly from the verified Trezor website to avoid phishing.
Step 3: Confirm Device Authenticity
The app automatically verifies your device firmware. If any mismatch appears, abort the process immediately.
Step 4: Enter Your PIN Securely
Use the randomized PIN grid displayed on your device. This dynamic entry prevents malware-based keyloggers.
Step 5: Access Your Wallet Dashboard
After authentication, your portfolio appears in Trezor Suite where you can send, receive, or stake crypto safely.
🛡️ Why Trezor Login Is the Gold Standard for Crypto Security
The Trezor Login system offers a blend of security and simplicity. Here’s why it’s considered a benchmark in digital asset protection:
- 🔒 Offline Authentication: Login validation happens entirely on the hardware device, disconnected from the internet.
- 🧩 Open-Source Code: Every security mechanism is publicly auditable, promoting transparency.
- 🧠 Human-Centered Design: Easy navigation while maintaining military-grade security standards.
- 💾 Recovery via Seed Phrase: If your device is lost, your assets can be restored using your 12–24 word phrase.
- ⚙️ Firmware Validation: Each update must pass Trezor’s cryptographic signature verification.
🧱 Security Tips for Safe Trezor Login
Even though Trezor provides hardware-grade protection, user awareness plays an equally critical role. Follow these essential guidelines:
✅ Use Official Sources Only
Always download Trezor Suite and firmware directly from the Trezor.io domain.
✅ Keep Recovery Phrase Offline
Write down your recovery seed and store it in a fireproof, waterproof location. Never digitize it.
✅ Avoid Public Wi-Fi
Log in only on secure, private networks to minimize exposure to network-level attacks.
✅ Update Firmware Regularly
Firmware updates close vulnerabilities. Always verify signatures before installation.
⚠️ Common Login Errors and How to Fix Them
| Issue | Cause | Solution |
|---|---|---|
| Device Not Detected | Loose USB or missing drivers | Reconnect or reinstall Trezor Bridge software. |
| Login Page Frozen | Corrupt cache or outdated Suite version | Clear browser cache or reinstall Suite. |
| Incorrect PIN Attempts | Mismatched grid interpretation | Wait before retrying; follow on-device PIN layout carefully. |
🌍 After Logging In: Managing Assets with Trezor Suite
Once authenticated through Trezor Login, you gain access to a user-friendly dashboard. You can track your portfolio, swap tokens, connect to DeFi applications, and monitor performance — all while maintaining full key control.
“Your crypto security begins with you — Trezor just makes it safer.”
📚 Frequently Asked Questions (FAQs)
Q1: Do I need the internet for Trezor Login?
A: You only need it to access Trezor Suite; your authentication remains offline.
Q2: Can I use Trezor on multiple computers?
A: Yes, simply connect your device and authenticate. No data is stored locally.
Q3: What happens if my device is lost?
A: Restore your funds on a new device using your recovery phrase.
Q4: Is Trezor Login free?
A: Absolutely. There are no charges for using or logging in with your hardware wallet.
Take Control of Your Crypto with Trezor Login
With Trezor Login, your private keys stay protected in your hands. No intermediaries, no cloud risks — just pure, decentralized ownership and peace of mind.
Trezor – Security that empowers the future of finance.